The AI Never Writes Code. Not One Line.
You describe what you need. The AI produces a formal specification, not source code. No code is written, generated, or deployed to the server. The specification is data that the engine reads.
"I need a task manager."
"Tasks should have a title, description, status, priority, due date, and who it's assigned to."
"Three roles. Admins can do everything. Managers are a step below. Regular members can only see and edit their own tasks."
"Members can only edit the title, description, and status. And only if the task is still in draft, open, or in progress."
"Members can delete their own tasks, but only while it's still a draft."
"Tasks go through a workflow: draft, open, in progress, review, done. You can send something back from review to in progress."
app TaskManager
name "Task Manager"
base_path "/app"
entity Task
title: String, required
description: Text
status: Enum(draft, open, in_progress, review, done)
priority: Enum(low, medium, high, critical)
due_date: Date
assigned_to: Reference(User)
role admin
inherits manager
role manager
inherits member
role member
permissions admin on Task
create: true
read: all
update: all
delete: all
permissions member on Task
create: true
read: own
update: own, fields [title, description, status]
when status in [draft, open, in_progress]
delete: own
when status is draft
transitions Task.status
draft -> open: "Open Task"
open -> in_progress: "Start Work"
in_progress -> review: "Submit for Review"
review -> done: "Approve"
review -> in_progress: "Request Changes"| Title | Status | Priority | Due | |
|---|---|---|---|---|
| Update landing page | open | high | Mar 15 | Start Work |
| Write API docs | in_progress | medium | Mar 20 | Submit for Review |
| Fix login bug | draft | critical | Mar 10 | Open Task Delete |
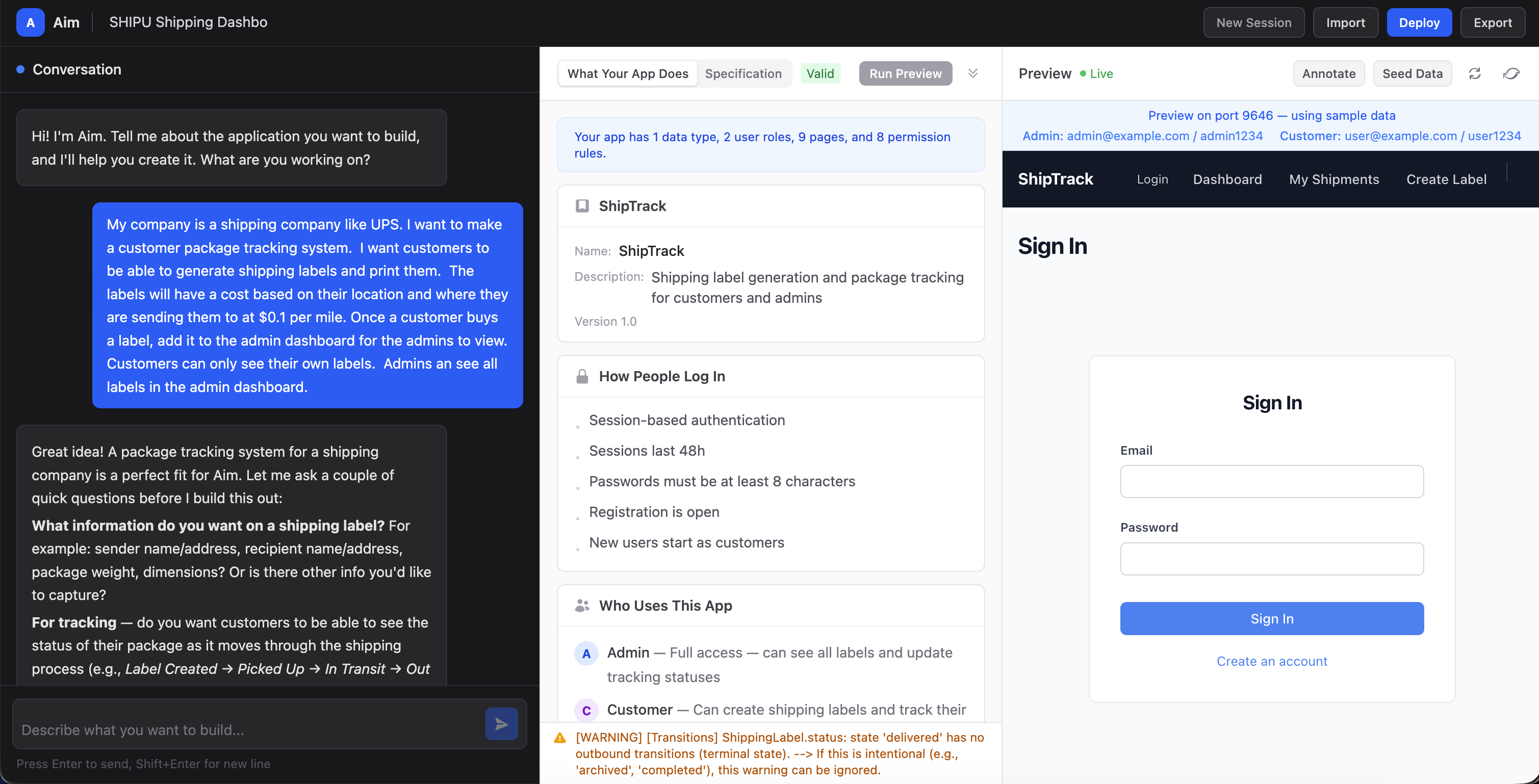
See the Real Interface
This is what it actually looks like. A conversation on the left, the specification in the middle, and the live application on the right.
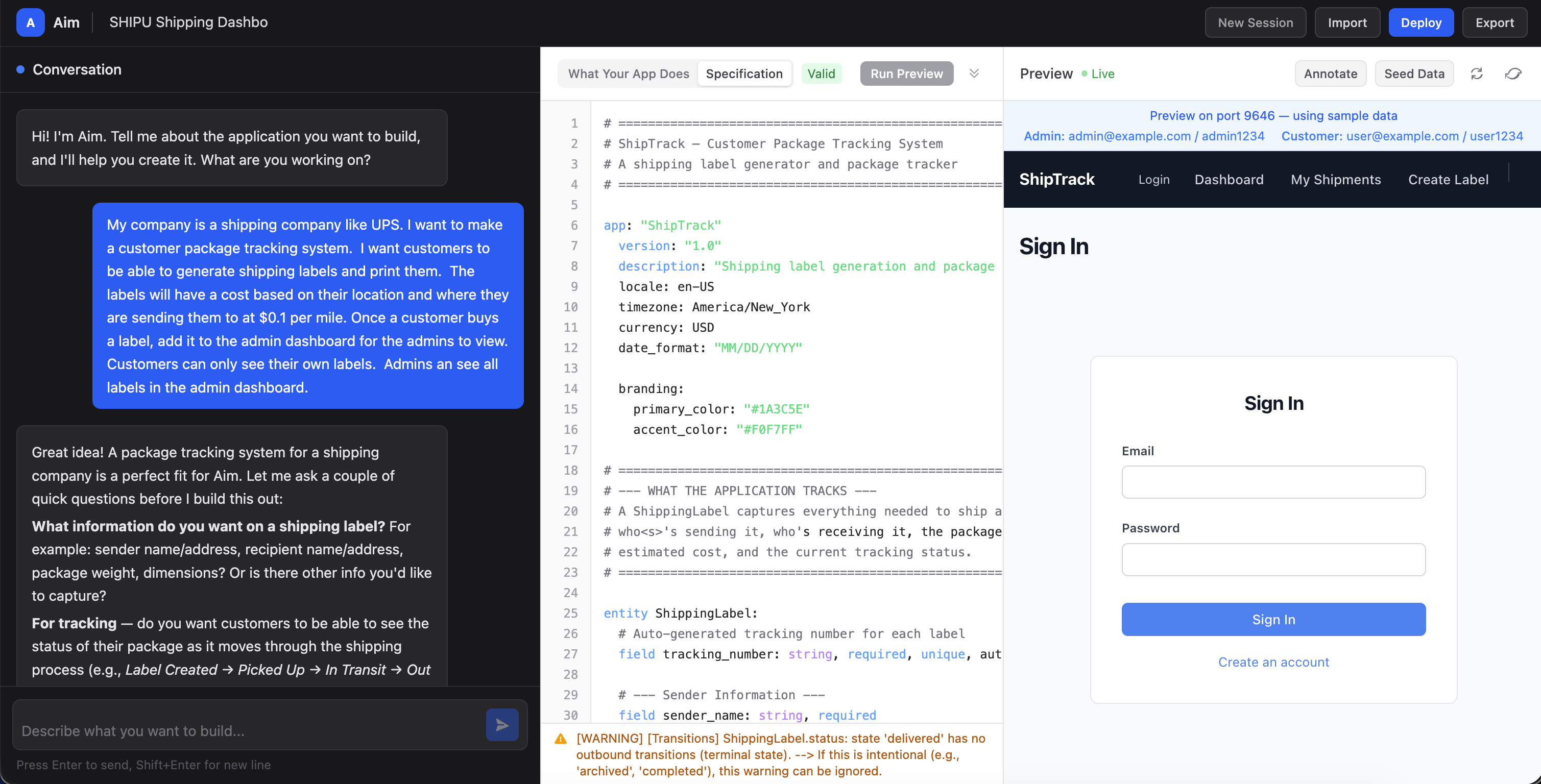
Finite Vocabulary
Entities, roles, permissions, transitions, validations, integrations, pages, events. That's it. No arbitrary computation, no memory operations, no file system access, no dynamic code execution.
Declarative, Not Imperative
The specification says what exists and what's permitted. It never says how to do anything. The engine handles all implementation.
AI Mistakes Are Visible
When an LLM generates source code, its mistakes become security vulnerabilities: injection flaws, broken access control, exposed data. When Aim's AI makes a mistake, it produces wrong data. A misspelled field name. A missing permission. Functionality errors, not security holes. The spec can't introduce SQL injection because it contains no SQL.